The dark web is well-known, and while it may sound like that seedy, smoky alleyway you try to avoid on your way home, it actually encompasses a lot of unexplored and non-searchable topics on your typical search engines.
While many of us rely on Google to find the information we require and get on with our lives, many people are unaware that only 4% of the internet is accessible to the general public via search engines. The remaining 96% is buried beneath the earth’s surface.
People are drawn to the dark web because it is hidden from the rest of the world, including your ISP and government agencies, making it a hotbed for illegal activity.
Many people mistake the deep web and the dark web for one and the same, but the two are not interchangeable.
The Deep Web
Most of the content on the deep web is information that you wouldn’t want to find through search engines.
As a general rule, the information you access can be found on the deep web whenever you log into an account and use any type of authentication, such as a username or password.
Before you get too worked up, keep in mind that this is a good thing, as the deep web protects your online personal information and privacy. In a nutshell, the deep web is where all the content that isn’t visible to search engines is stored.
In comparison to the dark web, the deep web is a relatively safe environment. Your information is relatively safe when you access the deep web, but that doesn’t mean it’s completely risk-free. Consider this: your data, such as personal account information, may contain a large number of passwords, which criminals will prize highly.
This is why, when accessing your account information online, you should use a virtual private network, also known as a VPN, which will encrypt your data and protect you.
The Dark Web
This is the other side of the coin, and it’s probably what most people think of when they hear the terms dark web and deep web, but they’re not the same thing. The deep web usually contains digitized records and harmless data, whereas the dark web is usually crawling with criminal activity.
Because regular browsers can’t access the dark web, you’ll need to use the Onion Router hidden service protocol. Tor servers are untraceable by traditional search engines, giving users complete anonymity while browsing the web.
Because of its high level of anonymity, the dark web attracts both benign and criminal online activity. This can range from complex puzzles to communities where people believe their right to free speech is under threat.
Some people may believe that taking their online communications to the dark web will help with anonymity, especially in light of recent revelations that major government organizations are snooping on users’ online movements.
Journalists and whistleblowers frequently use the dark web in order to exchange sensitive information.
In 2015, the dark web made headlines when it was revealed that Ashely Madison, a website designed that was designed for bored spouses to cheat on their partners, had 10GB of data stolen. However, this information was leaked on the Dark Web, with hackers threatening to publish it if the site continued to operate, which it finally did.
Some Shady Parts You Can Find on the Dark Web
Personal information that has been stolen is likely to end up for sale on the dark web if there has been an online data breach. This includes personal information such as social security numbers, bank account numbers, hacked Netflix accounts, and log-in credentials, among other things.
On the dark web, you can find a variety of illicit substances, including toxic chemicals, prescription drugs, and illegal drugs.
Human trafficking, counterfeit goods, body parts, guns, and even hired murderers are among the disturbing products and services available on the dark web.
Why is it Important to Use a VPN On the Dark Web?
Because the dark web contains illegal activity, you should be aware that being in the company of illegal content or illegal drugs can result in serious legal consequences. Silk Road, an online black market that sold illegal drugs, is an example of this.
The site was launched in 2011 and its total revenue is estimated to be around USD 1.2 billion. Ross Ulbricht, the company’s founder, was found guilty and sentenced to life in prison.
AlphaBay, another black market on the dark web, is another example. AlphaBay was founded in 2014 and quickly grew to be ten times the size of Silk Road, with a variety of goods ranging from breached data to illicit drugs. Alexandre Cazes, the company’s founder, was arrested and found dead in his Thai jail cell a few days later.
Users should keep in mind that the dark web is full of people and things they should avoid. Viruses that can be found on the dark web are included.
Hackers also frequent the dark web, where they can be hired. It should be noted that these individuals would be willing to compromise your devices in order to gain access to sensitive information.
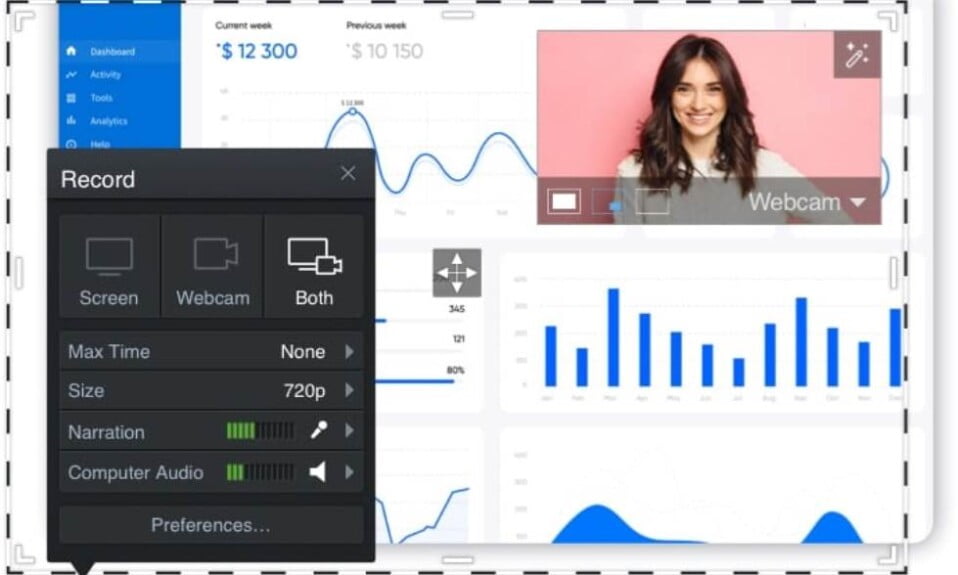
Webcam hijacking is a popular dark web tactic that involves a website attempting to gain access to your administrator tools, allowing them to take control of your webcam and spy on you in the privacy of your own home.
These are just a few of the reasons why people using the dark web require complete security. The best way to do so is to use a good VPN service.
Your ISP and the government will be unable to see your activity on the dark web, but they will be able to see that you are using the Tor Network, which may be enough to raise suspicions and have you monitored.
As a result, we strongly advise you to use a VPN when using Tor. Your internet traffic will be routed through your VPN before being routed through the Tor Network, allowing you to navigate the dark web freely and safely.
Your ISP and anyone else looking at your online activities will only be able to see your encrypted VPN traffic and will have no idea that you’re using Tor.
When using Tor over a VPN, one of the biggest concerns is that you’ll have to trust your VPN provider because they might be able to see what you’re doing. As a result, you’ll need to pick a VPN that doesn’t keep track of your online activities.
A trustworthy VPN for the dark web should accept bitcoin as payment, be Tor compatible, and not have any DNS leaks. It will also change your IP address, giving the impression that you are accessing the internet from a different location.
Because not all VPNs are created equal, it’s critical to use the right one when browsing the Dark Web. ExpressVPN is our top pick for the most secure VPN for the Deep Web. NordVPN is another more cost-effective option.
Which Dark Web Browsers are the Best?
Disclaimer
Please keep in mind that while using and browsing the Tor network is not illegal, you may become involved in illegal activities while online. These activities are neither condoned nor encouraged by us, and you do so at your own risk.
Make Tech Quick takes absolutely no responsibility for the decisions you make if you choose to use the information in this guide for anything other than educational purposes.
This further applies to any damages or incidents that occur while you’re online, such as being hacked or having your personal information stolen.
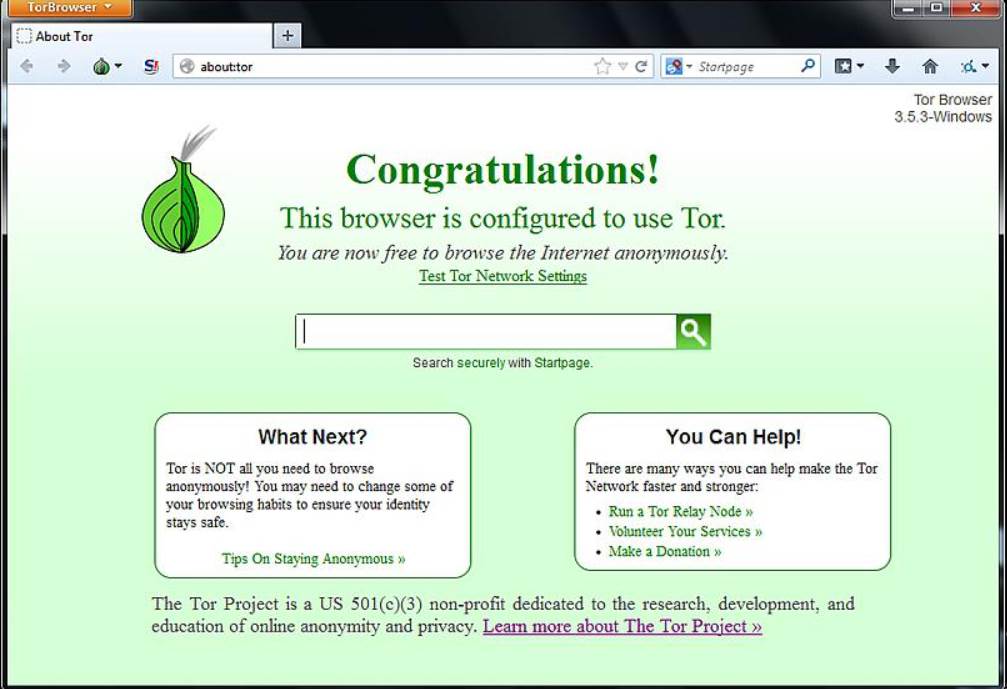
Tor Browser
It all started with a dark internet browser. You’ll always be using a version of this hidden web Browser to access the Tor Network, but it’s a good idea to stick with it for the most basic and simplistic browsing experience.
The Tor darknet Browser is a free, open-source deep browser for Windows, Mac, and Linux computers, as well as Android smartphones and tablets.
This was the first Deep Web browser of its kind, and it’s one of the safest and most secure ways to start using an anonymous deep web browser to browse the Dark Web.
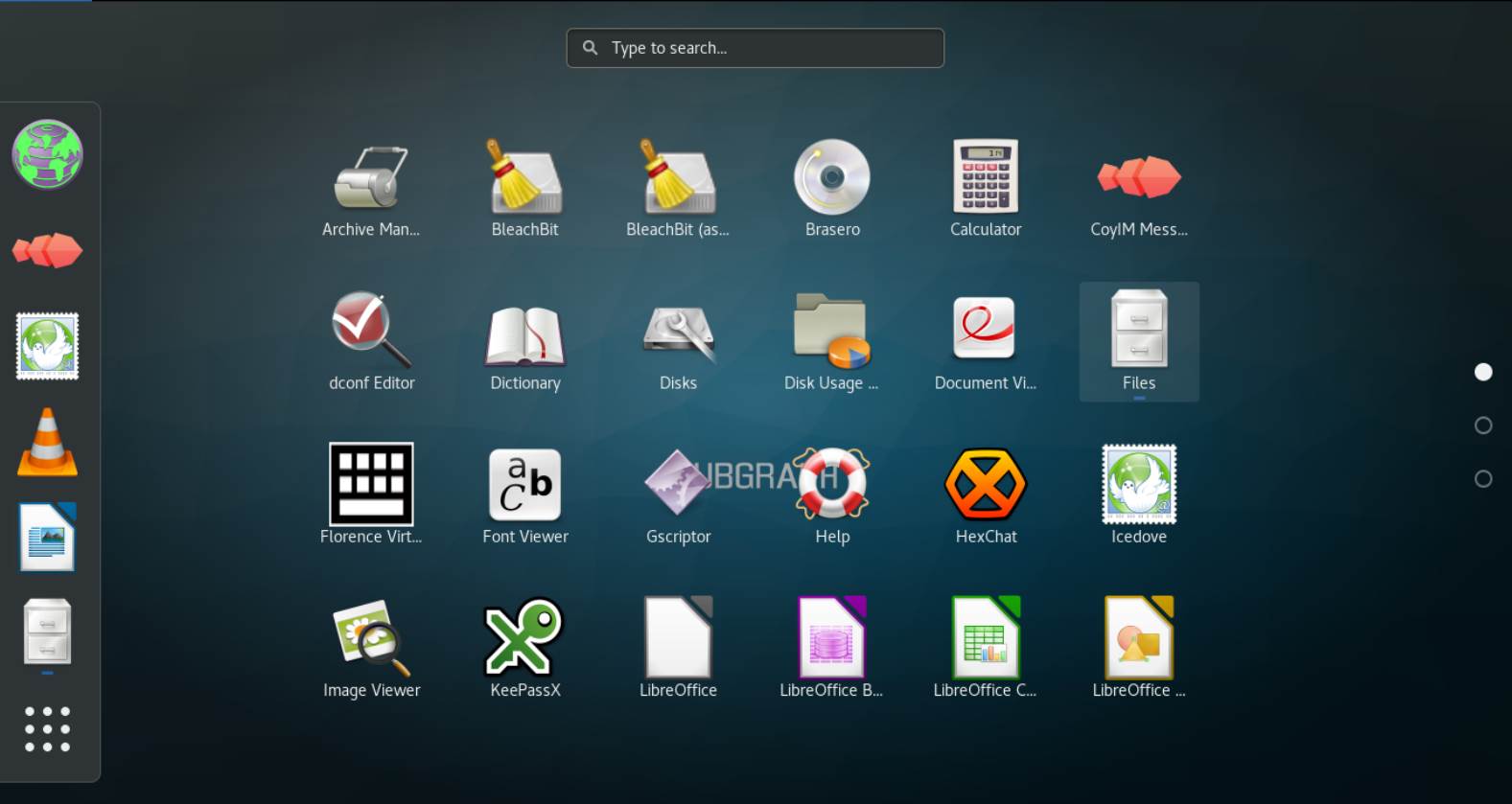
Subgraph OS
Subgraph OS is a deep web browser based on the Tor dark internet browser, and its main build is based on the same source code. It’s designed to help you access the internet in a free, private, and secure way that protects your safety and anonymity, as you might expect.
The Subgraph anonymous deep web browser, like the Krypton anonymous browser, is built with multiple layers, as are its internet connections to the Tor Network to aid in this. Kernal Hardening, Metaproxy, and FileSystem Encryption are some of the other platforms included in this build.
The ‘container isolation settings’ are another great feature of this deep dark web browser.
This means that any malware containers can be quickly isolated from the rest of your connection. This is useful if you’re instant messaging and receiving files and messages, using email, or dealing with other internet vulnerabilities.
This is easily one of the most popular dark web browsers available right now, and it’s well worth checking out if you want a secure and fast dark web experience.
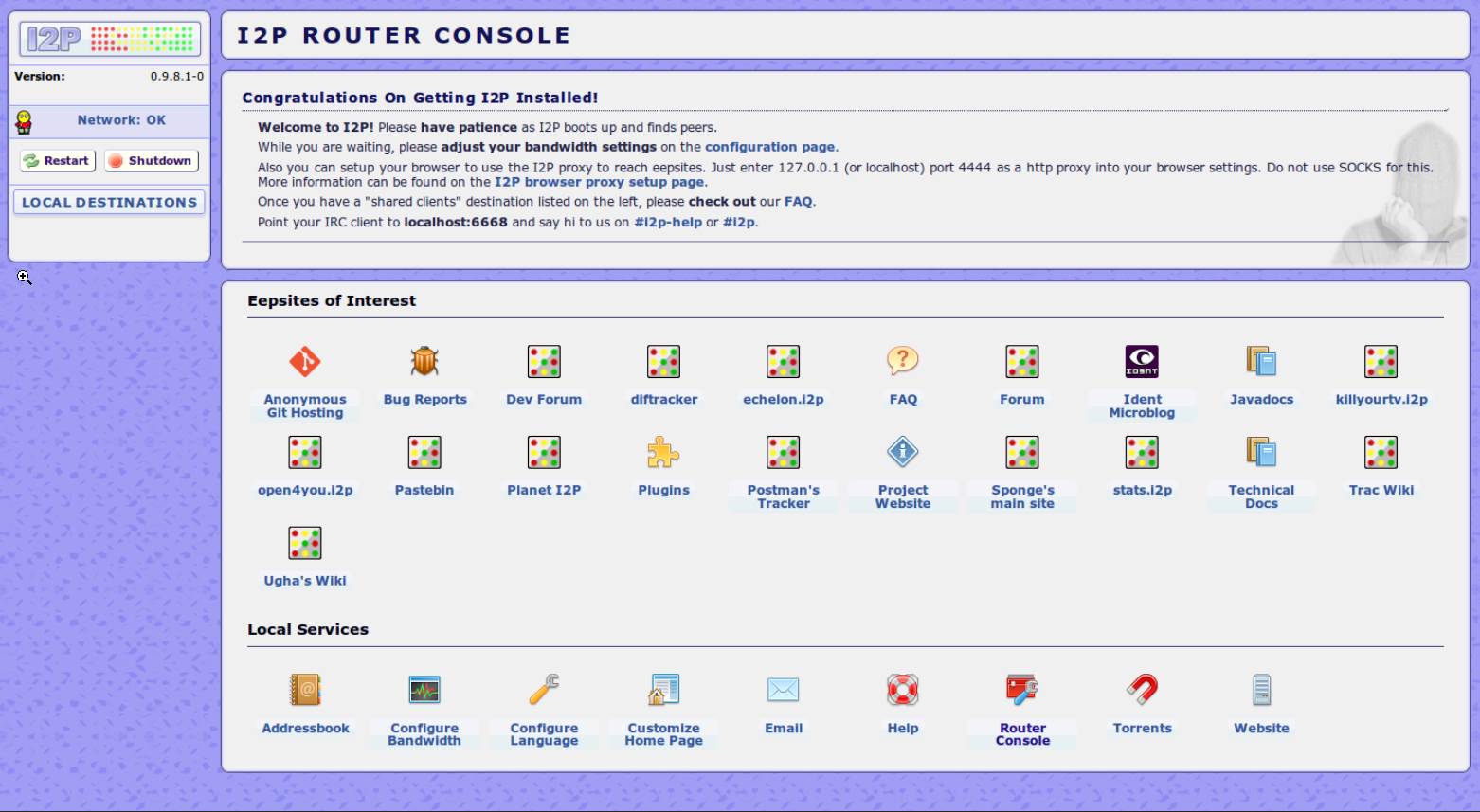
ISP – Invisible Internet Project
The Invisible Internet Project is a peer-to-peer (P2P) program that allows you to easily access both the surface and dark webs via a layered stream. It’s much more difficult to pinpoint and identify you because your data is muddled and masked by this constant stream of data.
This I2P browser supports both public and private keys, as well as Darknet technology and a decentralized file storage system to help users remain anonymous, similar to how Bitcoin works.
If you think this all sounds complicated, you’re right. The hidden web browser, on the other hand, does the job and is a great alternative to the Tor darknet browser if you don’t want to use Tor.
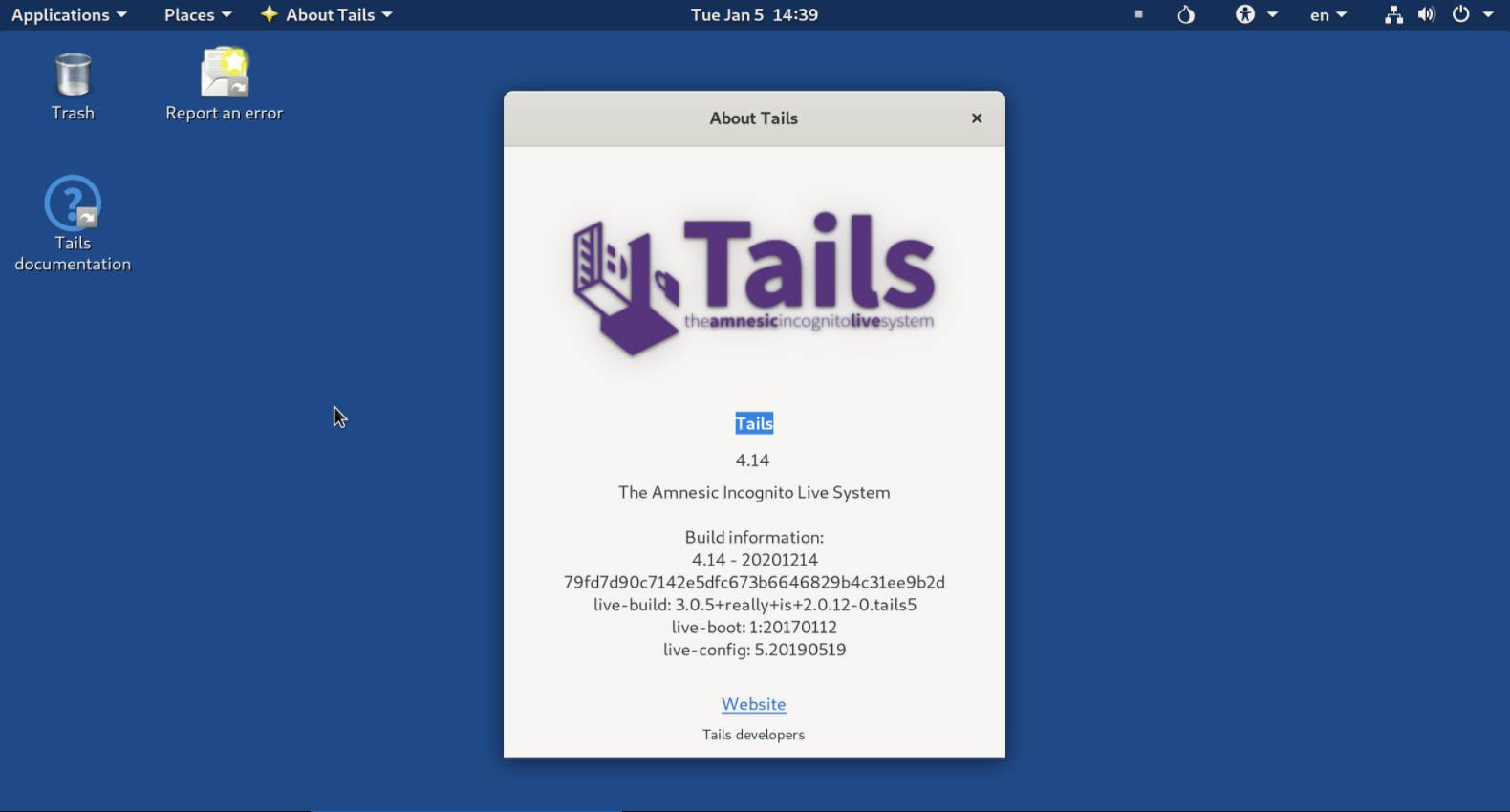
TAILS – The Amnesic Incognito Live System
The Tails darknet browser, like the vast majority of dark/deep web browsers, is based on the original Tor browser. This build, on the other hand, could be better described as a live operating system, given that it can be booted and accessed without installation from a USB stick or DVD.
Then, using advanced cryptographic tools, you can add the protective layers that ensure you remain anonymous while browsing the internet. All files, messages, videos, images, and emails sent and received to you and your accounts are included in this.
The Tails onion browser dark web will automatically shut down and temporarily halt the use of whatever OS you’re currently using to maximize your level of security while browsing, greatly reducing the risks of being discovered.
Of course, once the Tails system is shut down, everything will return to normal. Don’t worry, this OS runs entirely on RAM, leaving your hard drive and disc space unaffected. Despite the fact that Tor is the most popular hidden web browser, the Tails system is one of the best.
Firefox
Yes, we’re talking about the well-known dark browser, which is available for free and competes with Google Chrome, Opera, Safari, and other popular browsers.
All you have to do is go into the settings and tell your browser to connect to the Tor Network, which you should be able to find instructions for online.
However, you should download some additional privacy plugins, such as HTTPS Everywhere, before connecting to ensure you’re protected from malicious users. In this case, using a VPN can be extremely beneficial.
Waterfox
We should talk about Waterfox while we’re on the subject of Firefox. This is, obviously, a different version of the Firefox browser with the Mozilla connection turned off completely.
Furthermore, this anonymous deep web browser is capable of deleting all of your online information, as well as your passwords, cookies, and history, from your computer after each session.
While you’re browsing, it also automatically blocks trackers.
Despite a few significant differences from Firefox, many of the legacy plugins are still available for download and use. There are Windows and Android versions of this browser, and the dark internet browser community is still fairly active.
GNUnet
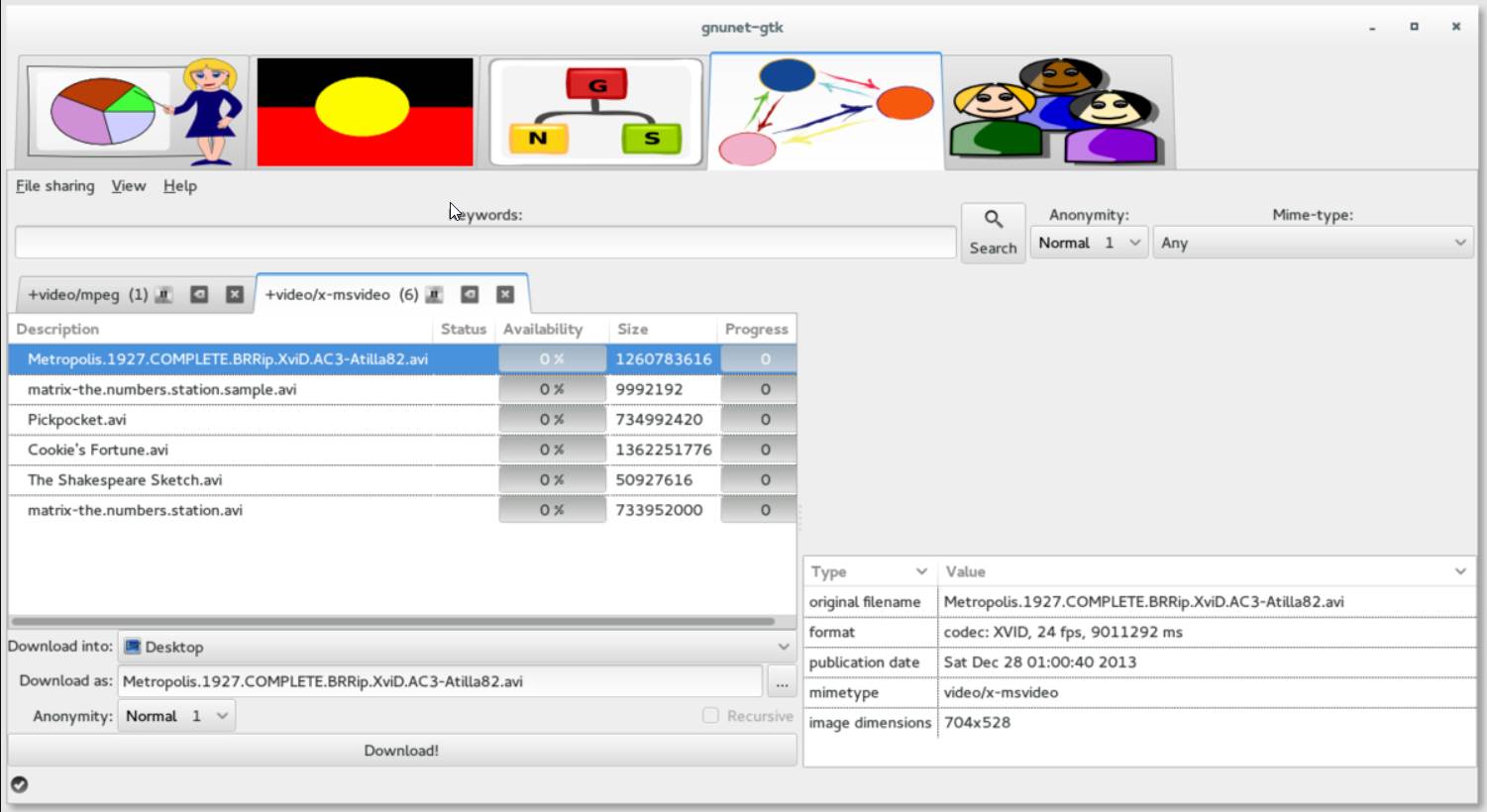
TCP, UDP, HTTP, HTTPS, WLAN, and Bluetooth are all used by GNUnet to provide decentralized, peer-to-peer communication.
Further, it informs users which other users they can trust and which they should avoid, protecting them from potential attacks. It safeguards sensitive data, and one of its main objectives is to keep the number of PII exposed to a minimum.
ZeroNet
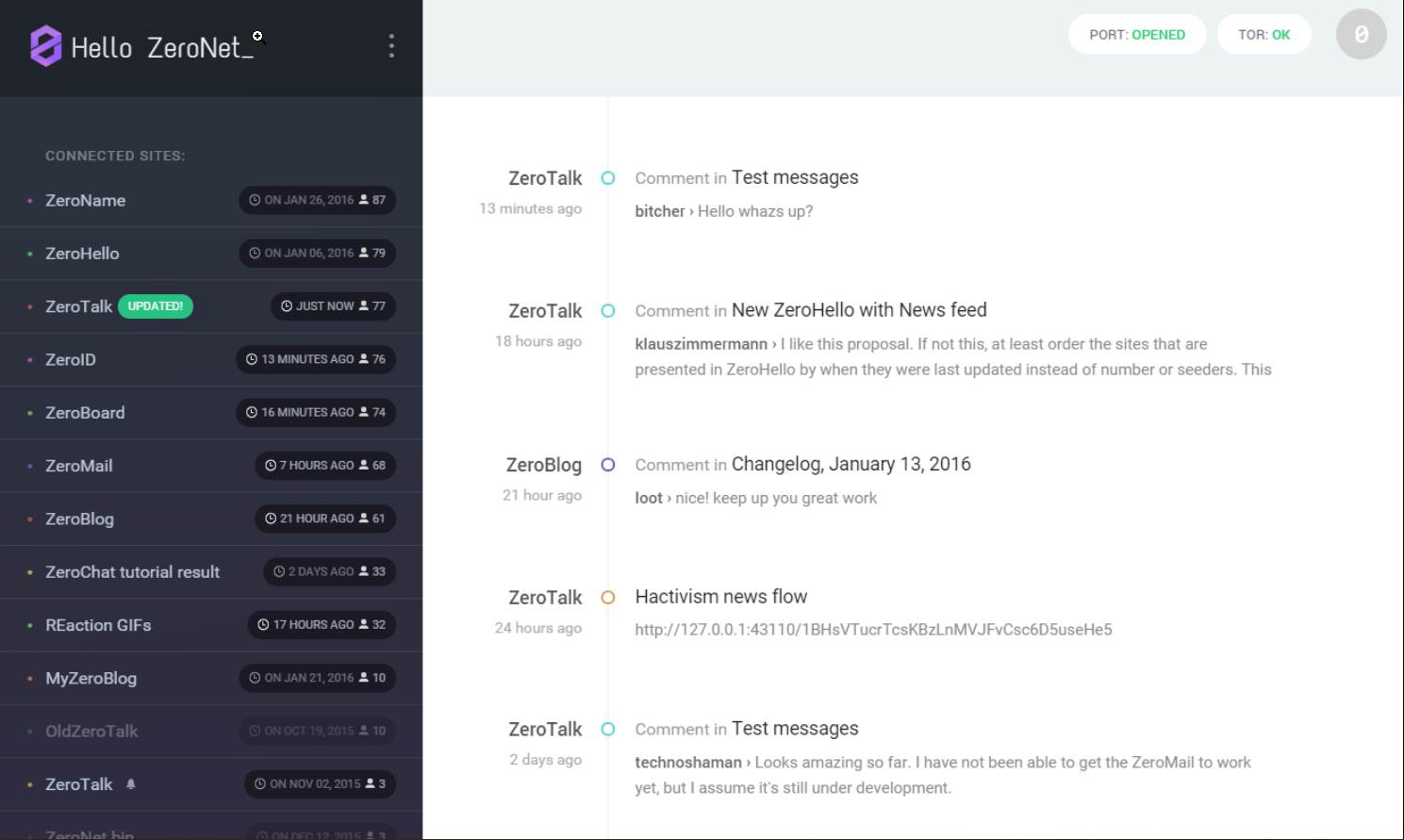
Another decentralized peer-to-peer communication tool is ZeroNet. It makes use of the BitTorrent network and Bitcoin cryptography. It can be used to share files and create websites. Sites are identified by a public key rather than an IP address.
Although it is not a completely anonymous networking platform, it does allow connection to the Tor Network, as do many others – though this may slow it down a bit.
Last but not least and interestingly, you can use Zeronet without an internet connection.
We attempted to give you a better understanding of what a good deep/dark web browser is like. It may be difficult to choose one from a plethora of web browsers if you are just getting started with the deep/dark web.
Whonix
The Whonix browser is the final dark/deep web browser we’ll look at today. This is another widely used browser that is based on the Tor Browser’s source code, so you can expect a similar connection and experience.
When it comes to the levels of security you get when using this browser, however, there are significant differences. Because this browser is so fast and uses the Tor network, it doesn’t matter if malicious code or software has root access; the DNS connection is so secure that it won’t be able to track you, especially if you use a VPN.
What you’ll also appreciate about the Whonix browser is that it allows you to not only connect, but also to set up and manage your own Tor server. Everything you’ll need is right in your browser, and it can even be run on a virtual machine.
There is a slew of other fantastic features in this browser, but they’re all detailed on the Whonix website. In short, Whonix could be for you if you want a powerful Dark Web experience with all the bells and whistles.
Conclusion
In this article, we’ve compiled a list of the best Dark Web Browsers for surfing the web anonymously and safely.
If you come across any other dark web browsers, please let us know in the comments section so we can check them out and update the list.
In this technological era, privacy is the most important concern, and cybercriminals are increasing their persistence attacks to steal users’ identities and personal information, which they then sell on dark web markets.
We have a number of Dark Web browsers listed here. Being an anonymous internet user will be extremely beneficial in terms of protecting your identity.
That’s all we have for you. We hope this guide about the best dark web browsers helped you and you loved it as well. For more interesting stuff, don’t forget to check out our gaming, troubleshooting, and computing guides.