The use of Cross-Site Scripting (XSS) attacks is commonplace online. They can be used for various malicious purposes, such as spoofing user accounts, stealing sensitive data, or even defacing a website. What, then, is cross-site scripting (XSS) attack? What about it makes it so dangerous? What measures can be taken to avert XSS attacks?
What Is a Cross-Site Scripting Attack?
XSS, or cross-site scripting, is a type of web application security vulnerability that can be exploited by malicious actors to inject arbitrary client-side code or scripts into targeted websites.
An attack that can steal sensitive information or carry out unsolicited transactions at the expense of the victim is triggered when an unsuspecting user interacts with the infected web page.
XSS is a type of client-side script injection attack. By inserting malicious code into an otherwise legitimate web page or web application, the attacker hopes to trick the victim into running malicious scripts on their computer. Attacks are carried out when a victim accesses a malicious website or uses a malicious web application.
When a malicious script is executed, the user’s browser receives it via the web page or application. Forums, message boards, and comment sections on websites are common entry points for Cross-site Scripting attacks.
If user input is not properly sanitized before being used in the generated output, the web page or application is susceptible to cross-site scripting attacks.
The target browser then needs to interpret the user’s input. XSS attacks are feasible in CSS, as well as in VBScript, ActiveX, and Flash. However, JavaScript is where you’ll typically find them because it’s so integral to the typical web browsing experience.
How Do XSS Attacks Work?
The core of an XSS attack is the website’s lack of proper input validation. This indicates that the site is not properly filtering out HTML before accepting user input.
What’s wrong with this picture, exactly? Your web browser will not be able to distinguish between the original code and the injected code. In other words, a browser will render malicious scripts (JavaScript, VBScript, etc.) along with the actual website’s code if an attacker feeds them in, thinking they are legitimate.
Many factors, including the target, the script’s trigger, whether the payload is reflected only on the client-side or can be stored in the server-side database, and more, influence the specifics of a given cross-site scripting attack.
Types of Cross-Site Scripting Attacks
According to the manner in which the script is run and the attack is transmitted, cross-site scripting (XSS) attacks can be divided into three categories:
- Reflected XSS.
- Stored XSS.
- DOM-based XSS.
So what do these XSS attacks mean?
Reflected Cross-Site Scripting (XSS)
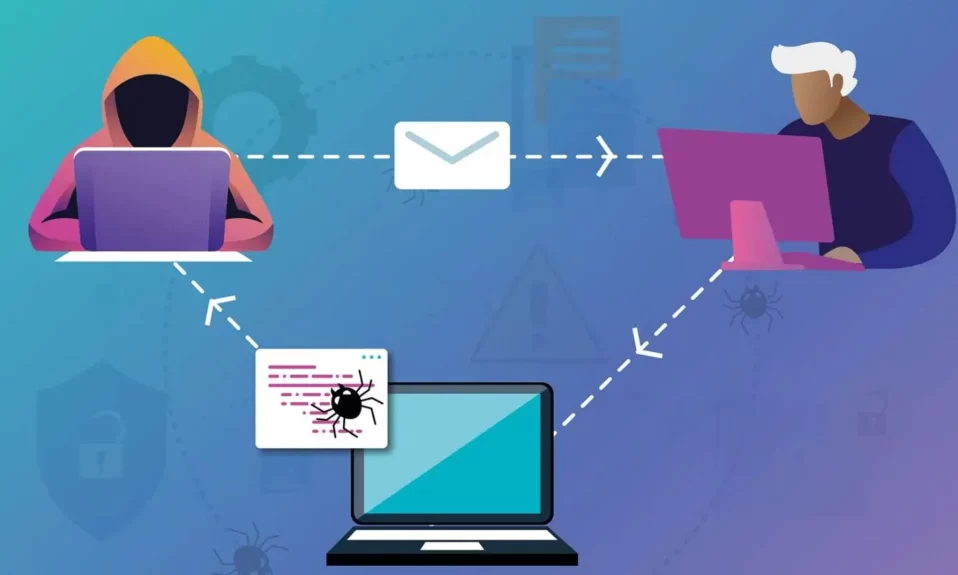
A specific type of XSS attack known as reflected cross-site scripting occurs when injected code is reflected off the server in any response that incorporates the input data from the original request made to the web server. The browser runs the script and sends the output to the client because the input validation was poor.
It is the most fundamental form of all XSS attacks, and compared to stored XSS, it poses less of a risk to a website. But it’s still a danger, so you should proceed with caution.
Reflected XSS attacks are typically spread through emails and other phishing or social engineering techniques.
Stored Cross-Site Scripting (XSS)
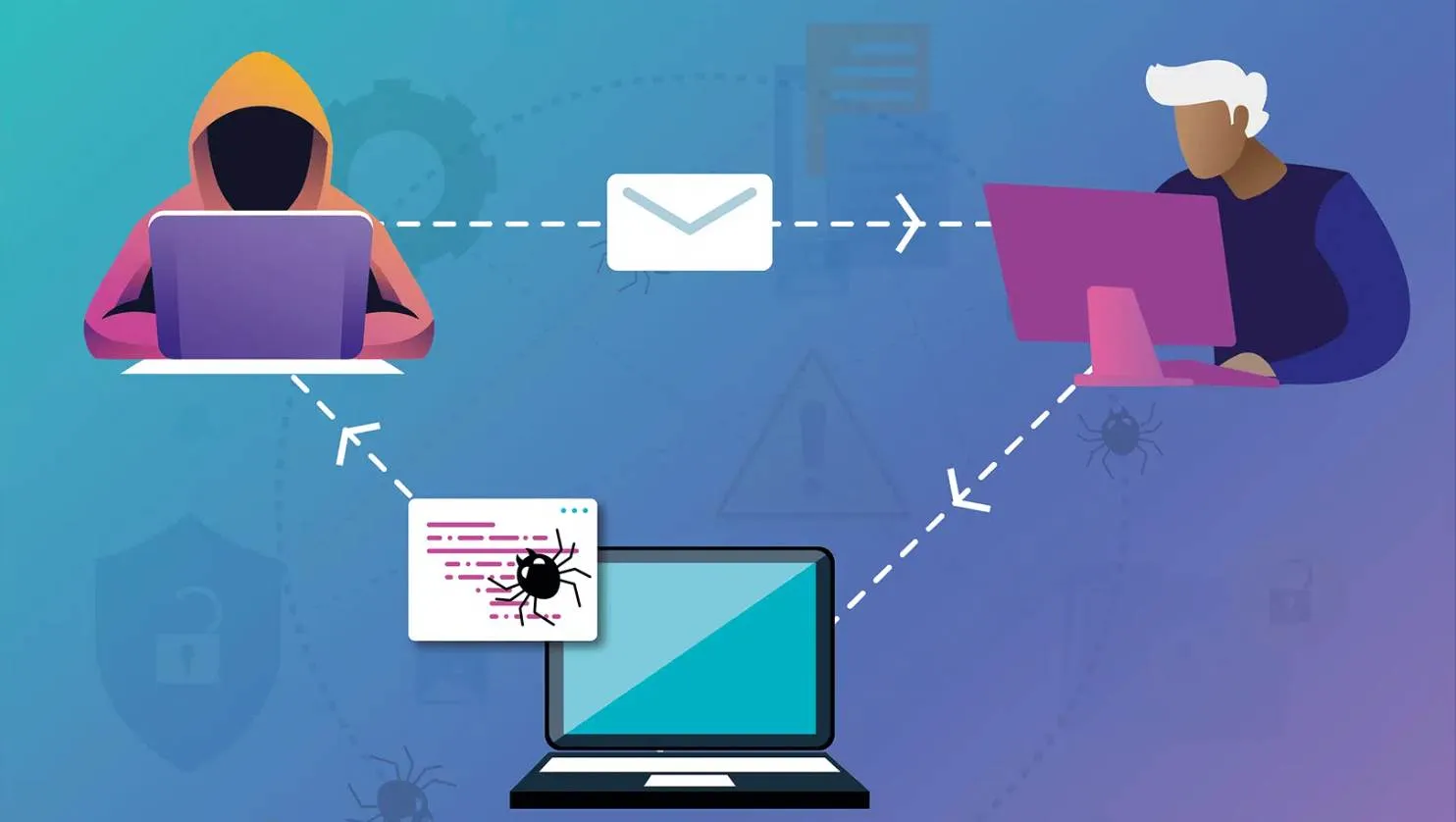
An XSS attack known as stored cross-site scripting allows for the storage or embedding of malicious code in a web server’s database. This is the deadliest kind of XSS attack because it may jeopardize the security of every user on the website. The payload will affect users who visit the web page that contains malicious code.
For instance, if the comment section of a well-known website was susceptible to stored XSS, an attacker could insert malicious code there. The malicious code would be executed by the viewer’s browser every time they encountered the comment, putting their system and data in danger.
The blind XSS attack falls under the stored XSS category. In this variation, the victim receives a reflection from another area of the web application after the attacker injects code as input, which is then stored in the backend.
When a website’s administrator checks the input data, for instance, if an attacker injects malicious code into the contact or feedback forms, the injected code will be executed.
DOM-Based Cross-Site Scripting (XSS)
A client-side attack known as a Document Object Model (DOM)-based cross-site scripting attack involves injecting malicious code into the browser’s DOM before the browser executes it. This occurs as a result of the website’s improper input sanitization.
An attacker can use a script to gain access to the DOM and change its content in a web application that is vulnerable. Similar to reflected XSS attacks, DOM-based XSS attacks are spread through social engineering. The victim is duped into visiting a vulnerable page by a malicious URL, where the browser executes the script.
How to Detect and Prevent XSS Vulnerabilities in Your Site
It is likely that the persistence of cross-site scripting (XSS) vulnerabilities is due in part to the difficulty with which they can be discovered and fixed. Avoiding cyberattacks and breaches that could cost you millions of dollars can be accomplished by adhering to good development practices and placing a high priority on security.
If you’re a web developer, you should know these things to keep XSS attacks at bay:
- As a general rule, user input should be disregarded. An XSS vulnerability is introduced whenever user input is rendered alongside the HTML.
- Use the appropriate escaping or encoding methods to protect against script errors in input fields.
- User input should be sanitized to prevent malicious scripts from being inserted.
- To protect cookies from being accessed by client-side scripting, set the HttpOnly flag.
- In order to prevent script injection into the web page from unauthenticated sources, it is important to implement Content Security Policy (CSP).
A user’s best defense against an impending XSS attack is a careful approach to selecting links to click on and websites to visit.
If you run an online business or blog, you should always be on the lookout for new defensive technologies to close any holes in your network’s defenses. If you’re a startup that can’t afford to significantly increase your security, the best security practices are the next best thing.